The smart Trick of Risk Management Enterprise That Nobody is Discussing
Table of ContentsAll About Risk Management EnterpriseThe Ultimate Guide To Risk Management EnterpriseSee This Report on Risk Management EnterpriseFascination About Risk Management EnterpriseThe Main Principles Of Risk Management Enterprise The 4-Minute Rule for Risk Management EnterpriseRumored Buzz on Risk Management Enterprise
Right here are some of its key attributes that facilities have to understand. So, have a look. Real-Time Threat Assessments and Mitigation in this software permit companies to continuously monitor and assess risks as they evolve. This feature leverages real-time information and computerized analysis to recognize prospective threats quickly. When threats are identified, the software assists in prompt reduction actions.
They deal with the obstacle of ongoing risk management by offering tools to keep an eye on threats continually. KRIs improve safety threat oversight, guaranteeing that possible threats are identified and managed successfully.
The 15-Second Trick For Risk Management Enterprise
IT run the risk of management is a part of enterprise threat management (ERM), designed to bring IT risk in line with an organization's danger cravings. IT risk monitoring (ITRM) incorporates the plans, procedures and modern technology essential to decrease hazards and vulnerabilities, while keeping compliance with relevant regulatory requirements. Furthermore, ITRM looks for to limit the repercussions of destructive occasions, such as safety violations.
Veronica Rose, ISACA board supervisor and a details systems auditor at Metropol Corp. The ISACA Danger IT framework straightens well with the COBIT 2019 structure, Rose stated.
Business Risk Management Software Application Growth: Perks & Characteristics, Expense. With technical developments, dangers are constantly on the surge. That being claimed, companies are most likely to face challenges that influence their funds, procedures, and online reputation. From swiftly fluctuating markets to governing changes and cyber dangers, companies navigate through a regularly transforming sea of threats.
The Risk Management Enterprise Statements
In this blog site, we will dive right into the globe of ERM software program, exploring what it is, its advantages, features, etc so that you can build one for your service. Enterprise Threat Monitoring (ERM) software is the application program for planning, routing, arranging, and managing company activities and streamlining risk monitoring processes.
With ERM, companies can make informative decisions to boost the overall durability of business. Read: ERP Application Growth Committed ERM systems are critical for businesses that consistently handle large amounts of delicate details and several stakeholders to accept strategic decisions. Some markets where ERM has ended up being a typical system are healthcare, finance, building, insurance, and info modern technology (IT).
: It is stressful for any enterprise to undertake an extensive audit. However, it can be avoided by utilizing the ERM software system. This system automates law conformity monitoring to keep the company secure and compliant. Besides that, it also logs and classifies all the files in the system making it much easier for auditors to examine processes much quicker.
Some Known Questions About Risk Management Enterprise.
You can additionally link existing software program systems to the ERM via APIs or by adding data by hand. Organizations can use ERM to assess threats based on their possible influence for far better risk management and mitigation.: Including this feature allows customers to obtain real-time notices on their devices about any type of risk that could happen and its impact.
Rather, the software program enables them to set limits for different procedures and send out push notices in instance of feasible threats.: By integrating information visualization and reporting in the personalized ERM software application, services can gain clear understandings about threat patterns and performance.: It is required for organizations to adhere to industry compliance and regulative requirements.
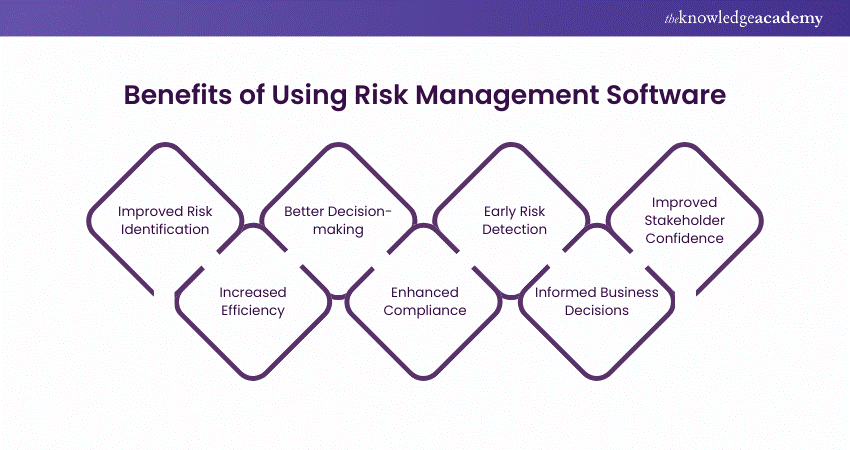
These platforms allow companies to apply best-practice threat management procedures that align with sector requirements, offering an effective, technology-driven method to recognizing, assessing, and mitigating threats. This blog site discovers the advantages of automated threat monitoring tools, the areas of danger administration they can automate, and the worth they give an organization.
Risk Management Enterprise Fundamentals Explained
Groups can set up forms with the appropriate areas and conveniently produce various types for various risk types. These danger analysis forms can be distributed for conclusion using automated workflows that send out alerts to the appropriate personnel to finish the kinds online. If forms are not completed by the due date, after that chaser emails are instantly sent out by the system.
The control surveillance and control screening process can additionally be automated. Firms can make use of computerized operations to send regular control examination notifications and staff can get in the results through on-line forms. Controls can likewise be kept track of by the software by establishing rules to send out notifies based upon control information kept in other systems and spreadsheets that is drawn into the system using API assimilations.
Threat monitoring automation software program can also support with risk coverage for all levels of the venture. Leaders can check out reports on danger exposure and control efficiency through a selection of reporting outputs consisting of static records, Power BI interactive reports, bowtie analysis, and Monte Carlo simulations. The capability to pull her comment is here genuine time reports at the touch of a switch removes difficult data adjustment jobs leaving risk teams with even more time to assess the data and encourage business on the finest strategy.
The need for efficient has actually never been more important. Risk Management Enterprise. Organizations operating in competitive, fast-changing markets can not afford delays or inefficiencies in attending to prospective risks. Standard danger monitoring using hand-operated spreadsheet-based processes, while acquainted, typically cause fragmented information, time-consuming reporting, and a raised likelihood of human error. Automating the danger monitoring procedure with software application addresses these drawbacks.
Risk Management Enterprise Can Be Fun For Everyone
This makes sure danger registers are always existing and aligned with business purposes. Conformity is another essential driver for automating danger monitoring. Criteria like ISO 31000, CPS 230 and COSO all offer advice around threat administration best techniques and control structures, and automated threat administration tools are structured to align with these needs assisting companies to satisfy most generally used threat administration requirements.
Look for risk software program platforms with a consents power structure to conveniently set up operations for threat acceleration. This performance allows you to customize the sight for each user, so they just see the information appropriate to them. Ensure the ERM software application provides individual monitoring so you can see who entered what data and when.
Go with a cloud-based system to make sure the system receives normal updates from the vendor including brand-new performance. Choose devices that use job threat administration capacities to handle your projects and profiles and the associated dangers. The benefits of adopting risk administration automation software program extend far past efficiency. Services that integrate these solutions right into their ERM strategy can anticipate a host of tangible and intangible.

The Best Strategy To Use For Risk Management Enterprise
While the situation for automation is engaging, implementing a danger management system is not without its challenges. For one, data quality is essential. Automated systems count on precise, up-to-date details to supply purposeful insights. To get rid of the obstacles of risk administration automation, organizations must spend in information cleaning and governance to ensure a strong structure for implementing an automated platform.
Automation in threat management empowers organizations to change their strategy to run the risk of and develop a stronger structure for the future (Risk Management Enterprise). The concern is no more whether to automate risk administration, it's how quickly you can start. To see the you can check here Riskonnect in action,
The answer frequently lies in exactly how well risks are anticipated and managed. Task monitoring software acts as the navigator in the tumultuous waters of job execution, offering devices that determine and assess dangers and devise strategies to minimize them anonymous effectively. From real-time data analytics to thorough threat monitoring control panels, these tools provide a 360-degree view of the task landscape, allowing job managers to make informed choices that maintain their projects on track and within budget.